Introduction
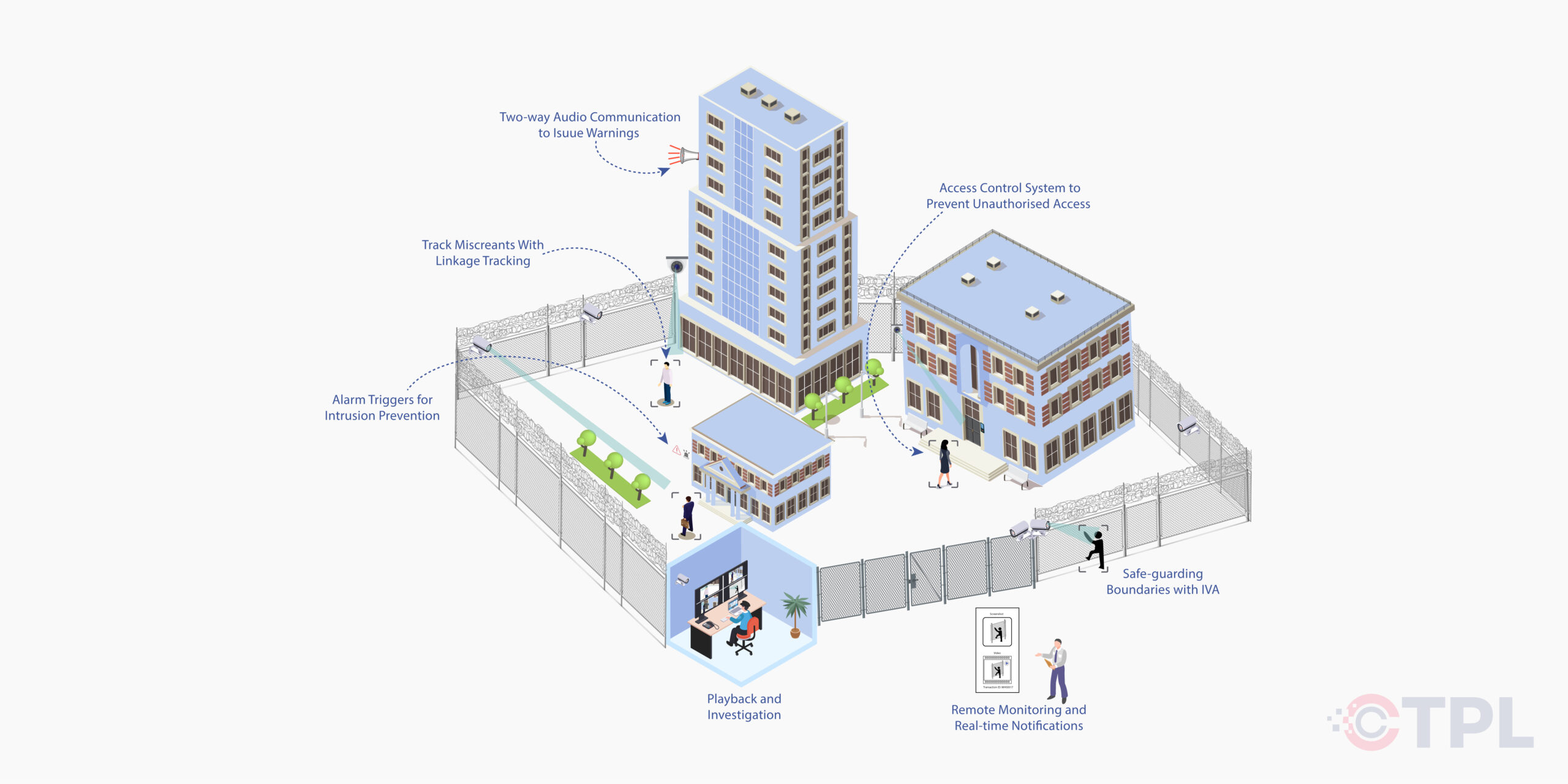
Ensuring robust perimeter security is crucial for safeguarding assets, information, and individuals against unauthorized intrusion. Matrix offers an advanced solution that establishes a strong first line of defense, detecting intrusions early, mitigating risks, and providing crucial evidence for effective response.
Perimeter security forms the first line of defense for any property, safeguarding its occupants, valuables, and critical infrastructure. It encompasses the strategies and technologies deployed to deter unauthorized entry, detect intrusions, and prevent potential threats from reaching your core assets.
How It Works
Perimeter security systems can be a layered approach, combining physical barriers, technology, and strategic placement to create a secure zone. Here are some common elements:
- Physical Barriers: Fences, walls, gates, and bollards act as a deterrent and physically impede unauthorized access.
- Distant Threat Detection: Matrix IP PTZ cameras with long-range capabilities and intelligent tracking ensure comprehensive monitoring of perimeters. Virtual boundaries set with Tripwire IVA trigger instant alerts upon breach, enabling proactive security measures.
- Access Control Systems: Electronic keypads, access cards, or biometric readers regulate authorized entry points.
- Intrusion Prevention: Customizable Intrusion Detection and Motion Detection IVA zones coupled with Alarm In/Out ports alert security personnel to unauthorized access attempts. Two-way audio communication and Loitering Detection further enhance deterrence and response capabilities.
- Intrusion Detection Systems (IDS): Sensors like motion detectors, vibration sensors, and buried cable systems can detect breaches or attempted intrusions.
- Playback and Backup: Matrix NVRs facilitate advanced video recording and management, supporting various playback modes for incident review. SATATYA SAMAS enables real-time monitoring and integrates seamlessly with other security systems for enhanced situational awareness.
- Video Surveillance Systems: Cameras with night vision, thermal imaging, or analytic capabilities monitor the perimeter and provide visual verification of security events.
- Alarm Systems: Triggered by breaches or suspicious activity, alarms notify security personnel and can deter intruders.
Drawbacks of Limited-Area Observation
Limited Intrusion Detection
Without advanced perimeter security, detecting and responding to intrusions promptly is challenging, leaving assets vulnerable.
Theft and Vandalism
Without adequate barriers and detection, intruders can easily access your property and steal valuables or cause damage. Unauthorized access can pose a risk to occupants, especially in areas with sensitive materials or equipment.
Lack of Proactive Alerts
Inability to set virtual boundaries and receive real-time alerts hinders timely intervention during security breaches.
Ineffective Incident Management
Without centralized monitoring and playback capabilities, investigating incidents and gathering evidence becomes inefficient and time-consuming.
Operational Disruptions
Security breaches can lead to downtime, production losses, and reputational damage.
Key Features Perimeter Security
- Long-Range PTZ Cameras: Enhanced with 42x optical zoom and 360° pan, ensuring comprehensive perimeter coverage.
- Intelligent Video Analytics (IVA): Tripwire and Loitering Detection for proactive alert triggers and enhanced security monitoring.
- Two-Way Audio Communication: Enables direct communication and warnings to potential intruders, enhancing deterrence.
- Alarm Integration: Alarm In/Out ports connect external sensors for immediate alert notifications and proactive response.
- Advanced NVR Capabilities: Supports flexible video playback and secure backup options for efficient incident review and evidence management.
- Integrated Solutions: Modern systems combine various elements like access control, intrusion detection, and video surveillance for a holistic security approach.ta.
-
Real-time Monitoring: Centralized platforms allow for real-time monitoring of the perimeter, enabling faster response times to security breaches.
- Automation: Automated features like alerts and access control procedures streamline security operations and reduce human error.e.
Advantages of Perimeter Security
- Early Intrusion Detection: Ensures prompt response to unauthorized access attempts, preventing security breaches.
- Proactive Security Measures: Real-time alerts and notifications enable swift action, enhancing overall security posture.
- Enhanced Deterrence: Two-way audio and loitering detection capabilities deter potential intruders, minimizing security risks.
- Efficient Incident Management: Facilitates quick retrieval and analysis of video footage for effective incident resolution and evidence gathering.
- Live Monitoring Capability: Allows real-time monitoring of all connected cameras across various locations, enhancing situational awareness and proactive security measures.
Conclusion
Perimeter Security
High Quality Products and Services
Maximize security with a reliable solution that minimizes false alarms and optimizes manpower deployment. Detects intrusions early with advanced video analytics and provides real-time alerts for faster response.

Project Series Bullet Network Cameras
Weather-proof Cameras for Outdoor Surveillance. 8MP Resolution, with Audio Support with IR Range 50m.

Project Series Dome Camera
Vandal-resistant Cameras for Complete Security

PTZ Network Cameras
360° Video Surveillance, 5MP Resolution, With Audio Support, IR Range 300m.

Enterprise NVR
Server-grade Network Video Recorders with Inbuilt Video Management Software.

High-Performance Network Video Recorders
Built with Robust Storage Technology, 8/16/32/64/96 Channel, 1/2/4/8 SATA Ports, 10TB/18TB Storage Support for Each.

SATATYA SAMAS
Video Management System that Meets Your Enterprise’s Surveillance Needs