Introduction
A mobile access control solution leverages smartphones and other mobile devices to manage and grant access to secure areas or resources. Instead of traditional keys or cards, users can use their mobile devices, equipped with digital credentials, to gain entry. This technology enhances security and convenience by enabling remote access management, instant credential updates, and integration with other digital systems. With features like Bluetooth, NFC, and biometric authentication, mobile access control solutions offer a flexible and scalable approach to modern security needs, supporting the growing trend of mobile-first business environments.
How it Works
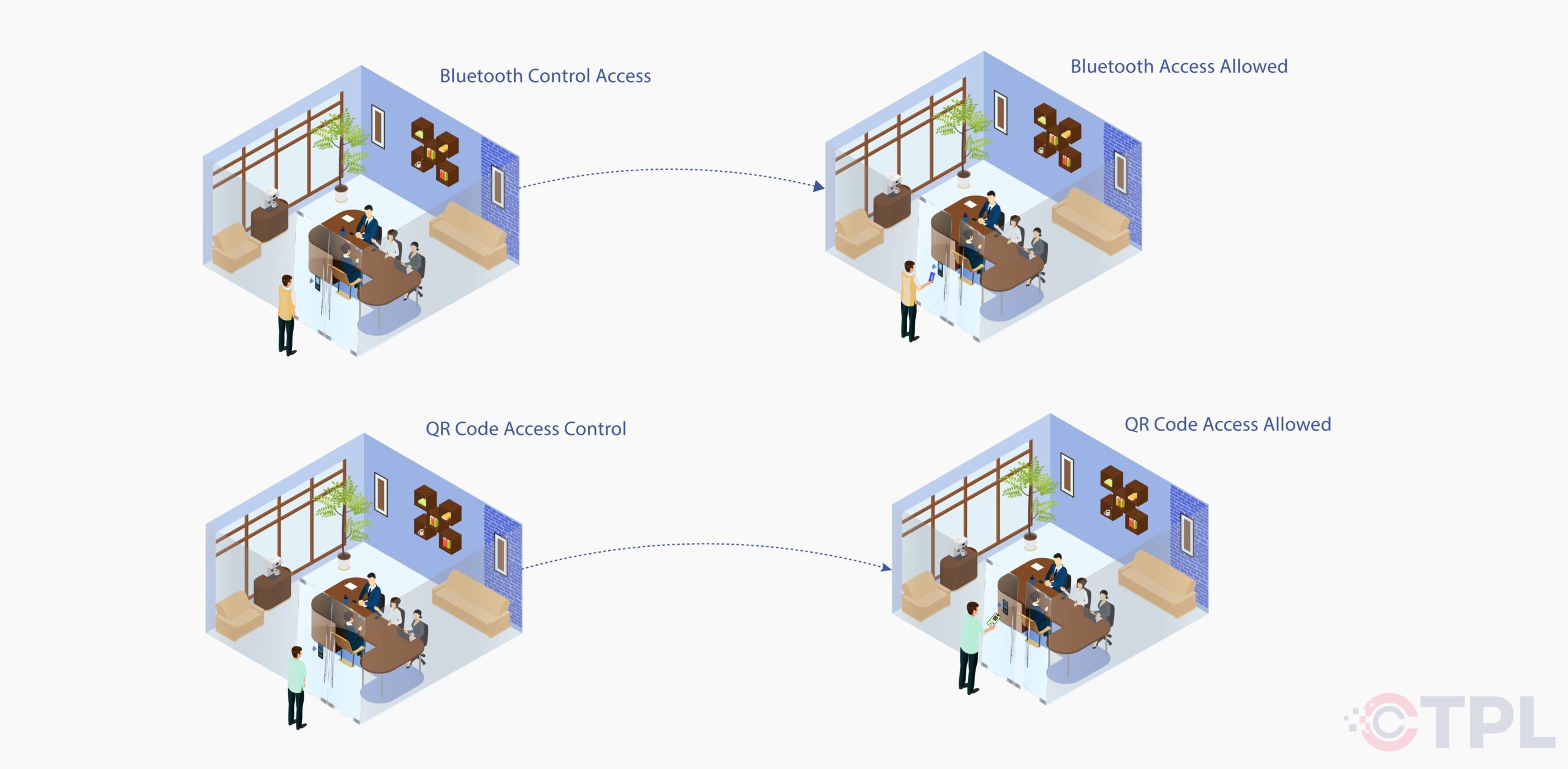
Bluetooth:
- Download the App: Employees install a secure app on their smartphones.
- Receive Credentials: Authorized users receive secure mobile credentials linked to their phones via Bluetooth.
- Approach the Reader: Users simply walk up to the access point with their smartphone in their pocket or bag.
- Automatic Authentication: The app automatically communicates with the reader using Bluetooth technology.
- Access Granted (or Denied): Based on valid credentials, the system grants or denies access.
QR Codes:
- Generate QR Codes: Authorized users are assigned unique, secure QR codes within the app or online portal.
- Scan the Code: Users approach the reader and scan the displayed QR code with their smartphone camera within the app.
- Secure Verification: The app transmits the QR code data for secure verification with the access control system.
- Access Granted (or Denied): Based on valid QR code and potentially additional verification (e.g., PIN), the system grants or denies access.
Key Features of Mobile Access Control Solutions
- Multi-Factor Authentication: Go beyond passwords. Combine phone possession with biometrics (fingerprint, facial recognition) or PINs for enhanced security.
- RFID Cards and QR code: Employs radio-frequency identification cards for quick and reliable access control.
- Mobile Credentials: Allows access via smartphones and other mobile devices.
- Real-time Monitoring: Tracks and records entry and exit in real-time for enhanced security oversight.
- Integration with Other Systems: Seamlessly integrates with other security and management systems.
- Secure Credentials: Issued mobile credentials are encrypted and tamper-proof, minimizing the risk of unauthorized access.
- Remote Access Management: Grant or revoke access remotely, eliminating the need for physical key management or card replacement.
Benefits of Mobile Access Control Solutions
- Effortless Access: Unlock doors with a simple tap, wave, or scan using your smartphone. No more fumbling for keys or remembering complex codes.
- Reduced Risk of Lost Credentials: Physical cards can be lost or stolen, compromising security. Mobile credentials are more secure and can be remotely revoked if needed.
- Enhanced User Experience: Provides a seamless and intuitive experience for users, making access control easy and efficient.
- Improved Operational Efficiency: Streamlines access management processes, saving time and resources.
- Streamlined Workflows: Employees gain instant access, eliminating delays and bottlenecks at entry points.
- Guest Management: Easily issue temporary access credentials to visitors through the mobile app, improving the visitor check-in process.
- Offline Functionality: Some systems allow access even with limited internet connectivity, ensuring smooth operation during network outages.
- Encrypted Communication: Mobile access control systems use secure protocols to transmit data between smartphones and readers, minimizing the risk of data interception.
Conclusion
Mobile access control solutions represent the future of secure and convenient access management. By integrating advanced security features with the convenience of mobile technology, these solutions provide a robust, flexible, and cost-effective way to manage access across your organization. Embrace the convenience and security of mobile access control to enhance your organization’s access management strategy and ensure the safety of your resources and personnel.
From the Services
High Quality Products and Services
There are many variations of passages of ipsum available, but the majority have suffered alteration in form

COSEC ARC DC200P
Two-Door Access Controller Innovated for New Age Organizations

COSEC ARGO FACE
Face and RFID Card Based Access Control and Time-Attendance Door Controller

COSEC VEGA Series
Finger and RFID Card Based Biometric Door Controller

COSEC PATH Series
Fingerprint-Based Access Control and Time-Attendance Door Controller

COSEC ATOM Series
Next Generation Readers Engineered for Simplifying Access Control

COSEC PANEL200P
Compact Access Controller Hub Pioneered for Advanced Security

COSEC ARC IO800
Compact Input-Output Controller Devised for Superior Control